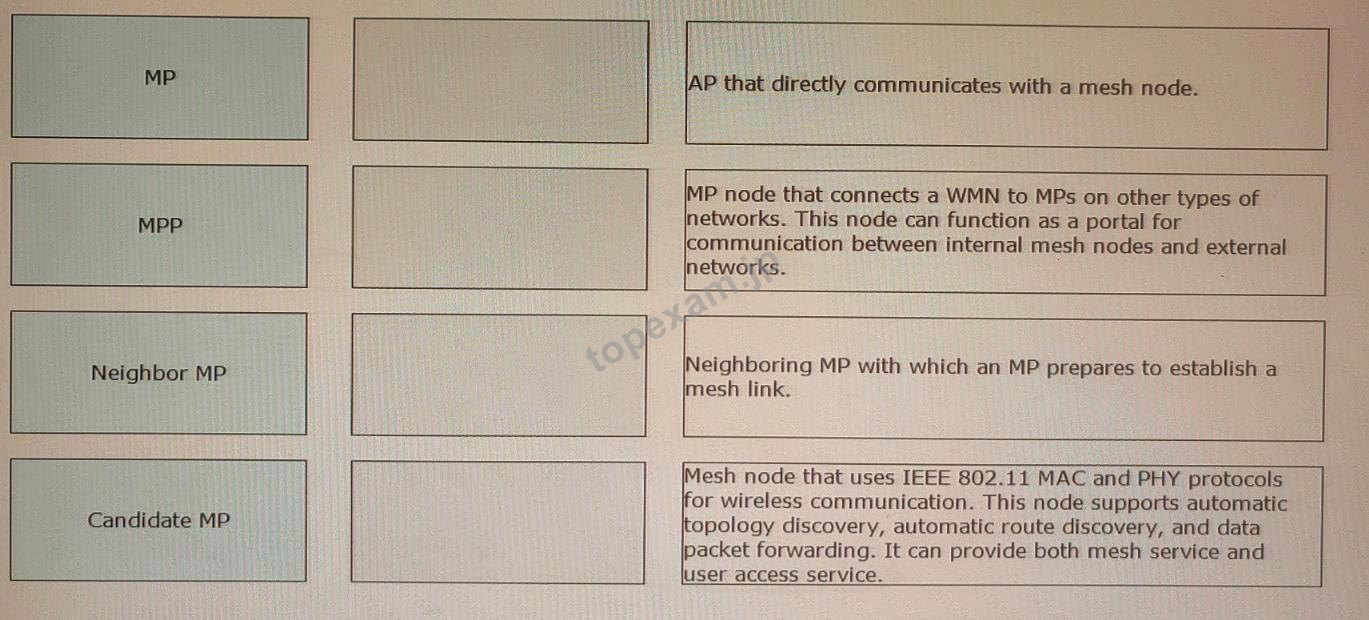
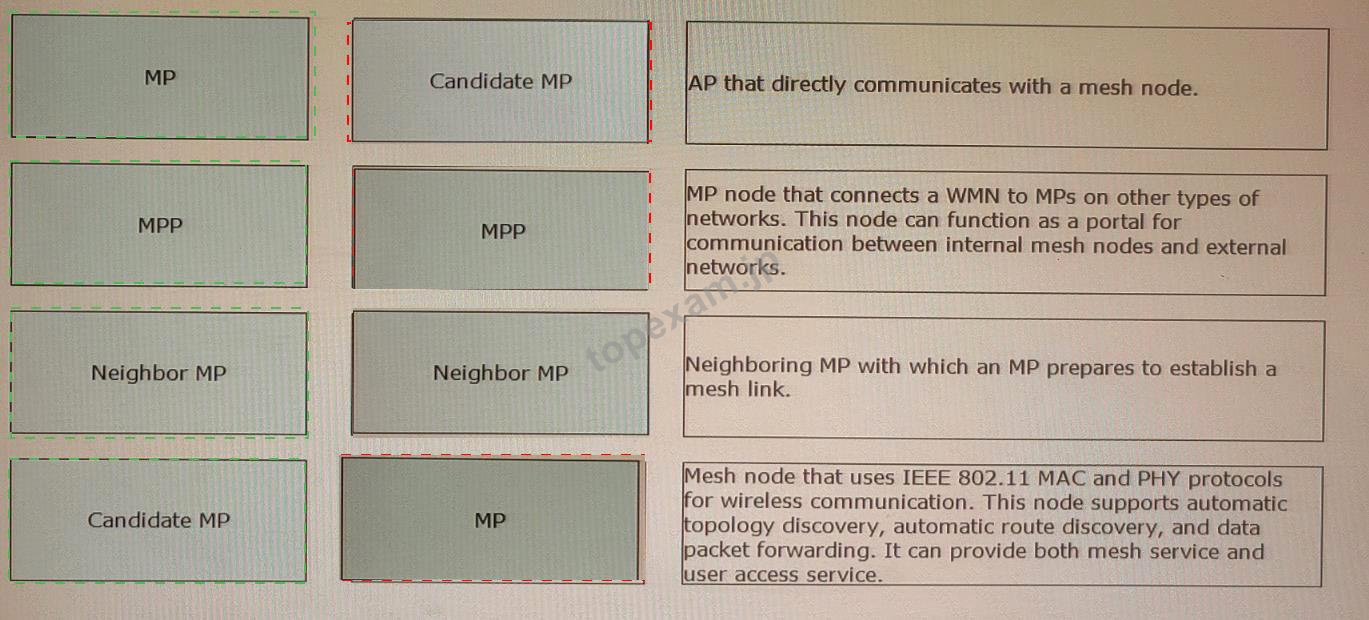
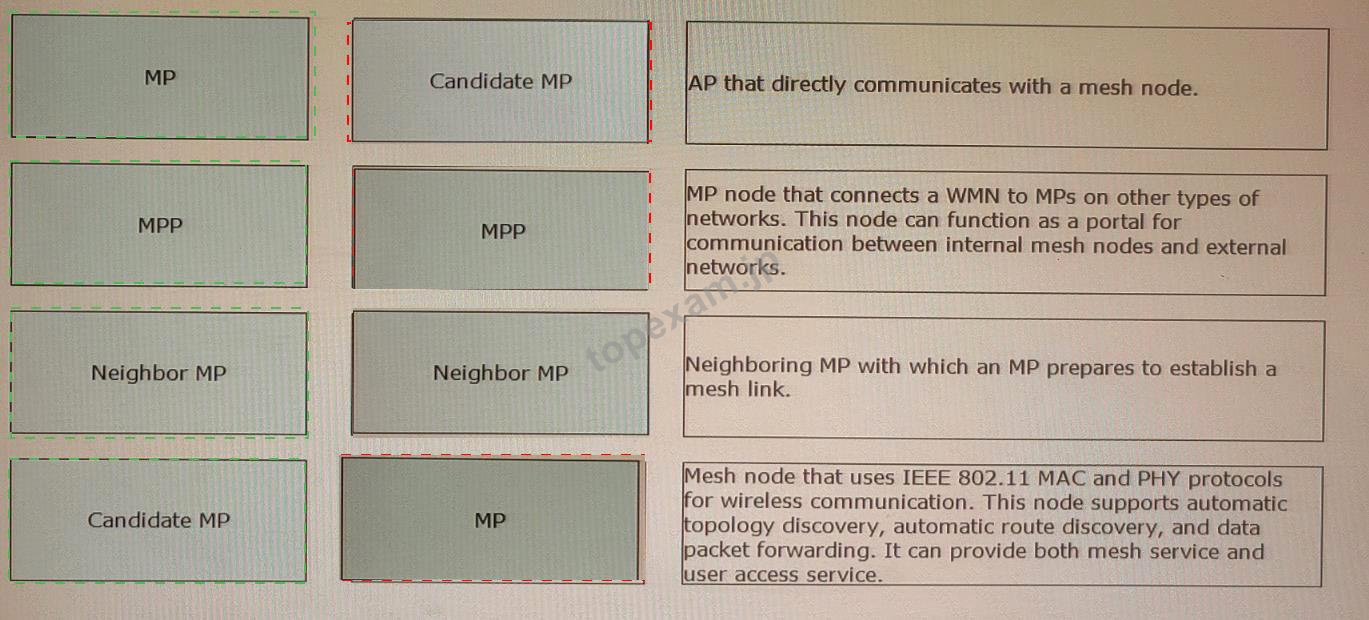
質問 1:In mesh networking, APs have different roles. Drag the AP roles on the left to the role descriptions on the right.
 正解:
正解:
Explanation
MP: Mesh node that uses IEEE 802.11 MAC and PHY protocols for wireless communication. This node supports automatic topology discovery, automatic route discovery, and data packet forwarding. It can provide both mesh service and user access service1.
MPP: MP node that connects a WMN to MPs on other types of networks. This node can function as a portal for communication between internal mesh nodes and external networks1.
Neighbor MP: Neighboring MP with which an MP prepares to establish a mesh link1.
Candidate MP: AP that directly communicates with a mesh node2.
https://support.huawei.com/enterprise/en/doc/EDOC1100064365/90f2391e/configuration-examples-for-mesh
2:
https://support.huawei.com/enterprise/en/doc/EDOC1100169459/8d79210e/configuring-wireless-mesh-networki
質問 2:iMaster NCE-Campuslnsight provides Intelligent radio calibration for high-load APs to increase the frequency bandwidth. This function applies to both 5 GHz and 2.4 GHz frequency bands.
A. False
B. True
正解:A
解説: (Topexam メンバーにのみ表示されます)
質問 3:Which of the following statements are true about data collection of IMaster NCE-Campuslnslght? (Select All that Apply)
A. The UTC time of iMaster NCE-Campuslnsight must be the same as that of its managed devices.
B. iMaster NCE-Campuslnsight uses telemetry to Implement efficient data collection.
C. Calculated data can be displayed on iMaster NCE-Campuslnsight only after a license Is loaded on the device management page.
D. To collect data from WLAN devices, ensure that WACs can communicate with the southbound IP address of iMaster NCE-Campuslnsight. APs do not need to communicate with the southbound IP address of iMaster NCE-Campuslnsight.
正解:B,D
解説: (Topexam メンバーにのみ表示されます)
質問 4:In a dual-link HSB scenario, after an AP sets up CAPWAP links with the active and standby WACs, which of the following types of packets does the AP periodically send to the WACs to detect link status?
A. DTLS
B. Join
C. Keepalive
D. Echo
正解:D
解説: (Topexam メンバーにのみ表示されます)
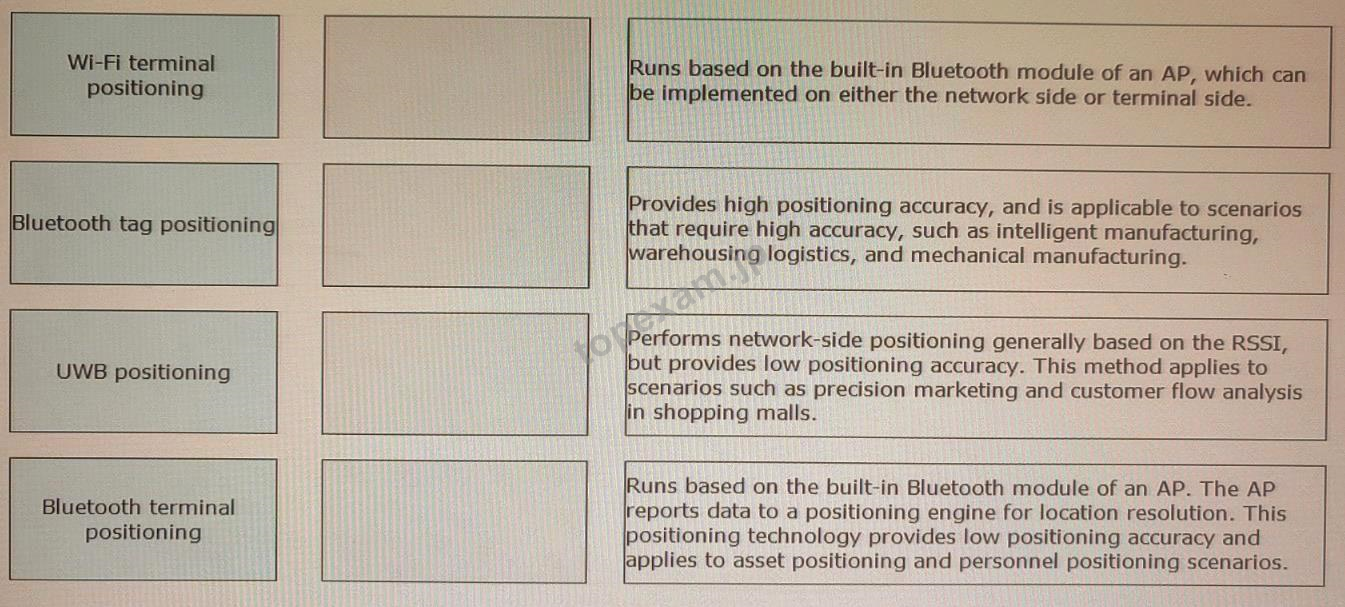
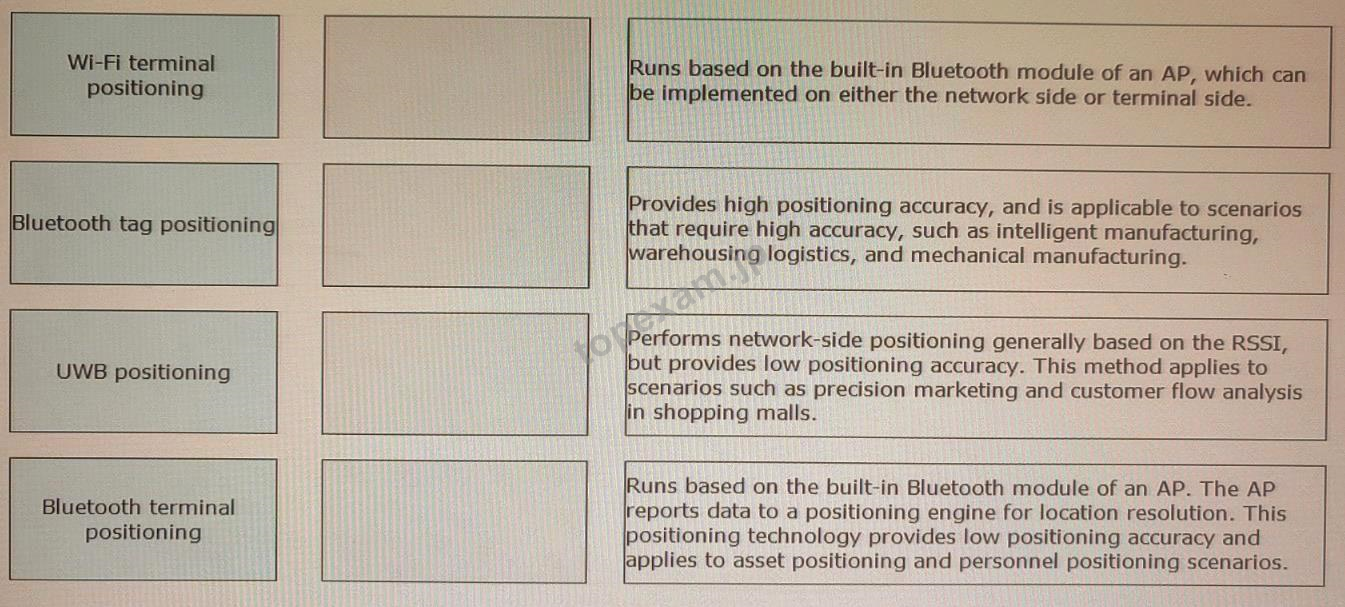
質問 5:Drag the Huawei's wireless positioning solutions on the left to their corresponding features and application scenarios on the right.
 正解:
正解:

Explanation
According to the Huawei documents and resources, the features and application scenarios of the wireless positioning solutions are as follows:
Wi-Fi terminal positioning: Performs network-side positioning generally based on the RSSI, but provides low positioning accuracy. This method applies to scenarios such as precision marketing and customer flow analysis in shopping malls.
Bluetooth tag positioning: Runs based on the built-in Bluetooth module of an AP. The AP reports data to a positioning engine for location resolution. This positioning technology provides low positioning accuracy and applies to asset positioning and personnel positioning scenarios.
UWB positioning: Provides high positioning accuracy, and is applicable to scenarios that require high accuracy, such as intelligent manufacturing, warehousing logistics, and mechanical manufacturing.
Bluetooth terminal positioning: Runs based on the built-in Bluetooth module of an AP, which can be implemented on either the network side or terminal side.
Therefore, Wi-Fi terminal positioning - 3, Bluetooth tag positioning - 4, UWB positioning - 2, Bluetooth terminal positioning - 1 is the correct answer. References: :
https://support.huawei.com/enterprise/en/doc/EDOC1100158948/9a0d5c37/wi-fi-terminal-positioning :
https://support.huawei.com/enterprise/en/doc/EDOC1100158948/9a0d5c37/bluetooth-tag-positioning :
https://support.huawei.com/enterprise/en/doc/EDOC1100158948/9a0d5c37/uwb-positioning :
https://support.huawei.com/enterprise/en/doc/EDOC1100158948/9a0d5c37/bluetooth-terminal-positioning
質問 6:Which of the following statements about EAP relay and EAP termination are false? (Select All that apply)
A. In EAP relay mode, an access device extracts information from EAP packets, encapsulates the information into RADIUS packets, and sends the RADIUS packets to an authentication server.
B. The EAP termination mode simplifies the processing on an access device and supports various authentication methods. However, this mode requires an authentication server to support EAP and have high processing capability.
C. In EAP termination mode, an access device encapsulates EAP packets sent by an 802. IX client Into RADIUS packets, without processing the data in the EAP packets.
D. In EAP termination mode, an access device extracts client authentication information from the EAP packets sent by a client and encapsulates the information using the standard RADIUS protocol. The access device supports only the EAP MD5-Challenge authentication method.
正解:B,C
解説: (Topexam メンバーにのみ表示されます)
弊社は無料Huawei H12-351_V1.0サンプルを提供します
お客様は問題集を購入する時、問題集の質量を心配するかもしれませんが、我々はこのことを解決するために、お客様に無料H12-351_V1.0サンプルを提供いたします。そうすると、お客様は購入する前にサンプルをダウンロードしてやってみることができます。君はこのH12-351_V1.0問題集は自分に適するかどうか判断して購入を決めることができます。
H12-351_V1.0試験ツール:あなたの訓練に便利をもたらすために、あなたは自分のペースによって複数のパソコンで設置できます。
安全的な支払方式を利用しています
Credit Cardは今まで全世界の一番安全の支払方式です。少数の手続きの費用かかる必要がありますとはいえ、保障があります。お客様の利益を保障するために、弊社のH12-351_V1.0問題集は全部Credit Cardで支払われることができます。
領収書について:社名入りの領収書が必要な場合、メールで社名に記入していただき送信してください。弊社はPDF版の領収書を提供いたします。
一年間の無料更新サービスを提供します
君が弊社のHuawei H12-351_V1.0をご購入になってから、我々の承諾する一年間の更新サービスが無料で得られています。弊社の専門家たちは毎日更新状態を検査していますから、この一年間、更新されたら、弊社は更新されたHuawei H12-351_V1.0をお客様のメールアドレスにお送りいたします。だから、お客様はいつもタイムリーに更新の通知を受けることができます。我々は購入した一年間でお客様がずっと最新版のHuawei H12-351_V1.0を持っていることを保証します。
弊社は失敗したら全額で返金することを承諾します
我々は弊社のH12-351_V1.0問題集に自信を持っていますから、試験に失敗したら返金する承諾をします。我々のHuawei H12-351_V1.0を利用して君は試験に合格できると信じています。もし試験に失敗したら、我々は君の支払ったお金を君に全額で返して、君の試験の失敗する経済損失を減少します。
弊社のHuawei H12-351_V1.0を利用すれば試験に合格できます
弊社のHuawei H12-351_V1.0は専門家たちが長年の経験を通して最新のシラバスに従って研究し出した勉強資料です。弊社はH12-351_V1.0問題集の質問と答えが間違いないのを保証いたします。

この問題集は過去のデータから分析して作成されて、カバー率が高くて、受験者としてのあなたを助けて時間とお金を節約して試験に合格する通過率を高めます。我々の問題集は的中率が高くて、100%の合格率を保証します。我々の高質量のHuawei H12-351_V1.0を利用すれば、君は一回で試験に合格できます。
TopExamは君にH12-351_V1.0の問題集を提供して、あなたの試験への復習にヘルプを提供して、君に難しい専門知識を楽に勉強させます。TopExamは君の試験への合格を期待しています。
Huawei HCIE-WLAN (Written) V1.0 認定 H12-351_V1.0 試験問題:
1. Either of the two APs that have established a mesh connection can send a Mesh Peering Close frame to the other AP to tear down the mesh connection.
A) False
B) True
2. Which of the following key factors is used by the CloudCampus cloud management platform to determine the tenant to which a device belongs?
A) Device ESN
B) Device IP address
C) Device model
D) Device MAC address
3. Which of the following items is not involved in the HLD phase?
A) Capacity planning
B) Network design
C) Deployment planning
D) AP position planning
4. To which of the following scenarios is radio calibration applicable?
A) Rail transportation scenario
B) WDS or mesh backhaul scenario
C) Enterprise office scenario
D) High-density scenario
5. Huawei Agile Cloud Authentication (HACA) supports only IMaster NCE-Campus as the HACA server.
A) False
B) True
質問と回答:
質問 # 1
正解: B | 質問 # 2
正解: A | 質問 # 3
正解: D | 質問 # 4
正解: D | 質問 # 5
正解: A |



 PDF版 Demo
PDF版 Demo







 品質保証TopExamは我々の専門家たちの努力によって、過去の試験のデータが分析されて、数年以来の研究を通して開発されて、多年の研究への整理で、的中率が高くて99%の通過率を保証することができます。
品質保証TopExamは我々の専門家たちの努力によって、過去の試験のデータが分析されて、数年以来の研究を通して開発されて、多年の研究への整理で、的中率が高くて99%の通過率を保証することができます。 一年間の無料アップデートTopExamは弊社の商品をご購入になったお客様に一年間の無料更新サービスを提供することができ、行き届いたアフターサービスを提供します。弊社は毎日更新の情況を検査していて、もし商品が更新されたら、お客様に最新版をお送りいたします。お客様はその一年でずっと最新版を持っているのを保証します。
一年間の無料アップデートTopExamは弊社の商品をご購入になったお客様に一年間の無料更新サービスを提供することができ、行き届いたアフターサービスを提供します。弊社は毎日更新の情況を検査していて、もし商品が更新されたら、お客様に最新版をお送りいたします。お客様はその一年でずっと最新版を持っているのを保証します。 全額返金弊社の商品に自信を持っているから、失敗したら全額で返金することを保証します。弊社の商品でお客様は試験に合格できると信じていますとはいえ、不幸で試験に失敗する場合には、弊社はお客様の支払ったお金を全額で返金するのを承諾します。(
全額返金弊社の商品に自信を持っているから、失敗したら全額で返金することを保証します。弊社の商品でお客様は試験に合格できると信じていますとはいえ、不幸で試験に失敗する場合には、弊社はお客様の支払ったお金を全額で返金するのを承諾します。( ご購入の前の試用TopExamは無料なサンプルを提供します。弊社の商品に疑問を持っているなら、無料サンプルを体験することができます。このサンプルの利用を通して、お客様は弊社の商品に自信を持って、安心で試験を準備することができます。
ご購入の前の試用TopExamは無料なサンプルを提供します。弊社の商品に疑問を持っているなら、無料サンプルを体験することができます。このサンプルの利用を通して、お客様は弊社の商品に自信を持って、安心で試験を準備することができます。
